IAR Embedded Secure IP
ユニークで柔軟なセキュリティにより、設計、生産、製造のあらゆる時点で既存製品を迅速にアップグレードすることができます。
01
アンチクローニング
ソフトウェア・アプリケーションとデバイス・ハードウェアの両方に対して固有の識別情報を生成し、偽造を防止すると同時に、製造プロセスの暗号化を行います。
02
アクティブIP 保護
安全なデバイスアクセスを確保する暗号化により、アプリケーション、ライブラリなどの知的財産のセキュリティを確実に守ります。
Visual Studio CodeによるIARの組込みセキュリティ
IAR Embedded Secure IPを使用して組込みシステムのセキュアなプロビジョニングおよびプログラミングを実現する 方法をご覧ください。IAR Embedded Secure IPは、あらゆるIDE およびコンパイラと互換性があり、Visual Studio Codeの拡張機能やCMakeなどの既存ツールに容易に統合することができます。(ビデオはすべて英語です)
IAR Embedded Secure IPの堅牢なIP保護およびクローニング防止を体験する用意はできていますか? 今すぐ評価版ソフトウェアをダウンロードして開始してください。
IAR Embedded Secure IPによるエンドユーザのメリット
1
開発後半での柔軟なセキュリティ設計
開発が途中まで完了している時点で、セキュリティ機能を組み込むことができます。それまでの設計やコードを変更する必要はありません。
2
メモリ要求の低いコード入力
小型メモリ搭載のフットプリントの小さなデバイスでもセキュリティ機能を実現できます。
3
サードパーティのライブラリやセキュアブート管理機能との統合
サードパーティのライブラリやセキュアブート管理機能を使用している場合でも、変更不要で、そのままIARのセキュリティ機能を利用できます。
4
ゼロトラストによるセキュアな製造
デバイスメーカが、ゼロトラストメーカにデバイスのプロビジョニングを委託する場合でも、すべてのプログラミングプロセスの安全性を確保することができます。
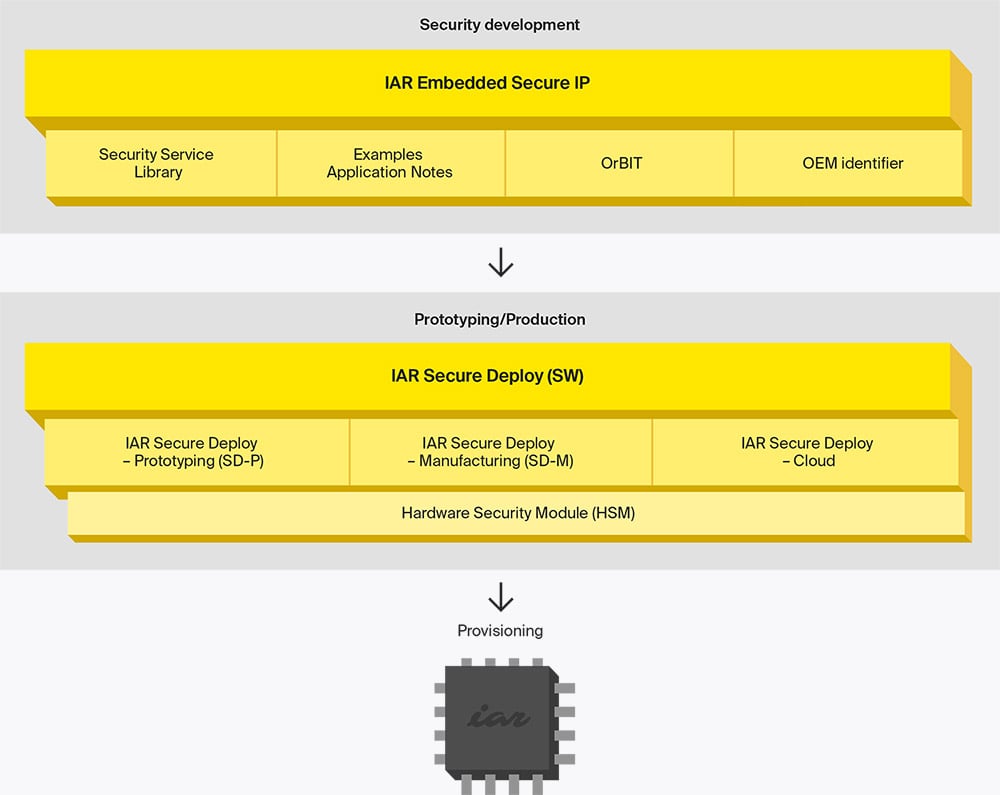
デバイス開発・製造の安全を確保
開発から製造までの全期間を通じてデバイスのセキュリティを保護することは非常に重要です。IAR Embedded Secure IPにはIAR Secure Deployが含まれており、あらゆる期間を通じてセキュリティをより効率的に実現できます。ここに示すツールの優れた機能とメリットにより、デバイスのセキュリティを確保しながら時間とコストを節約する方法をご覧ください。
製品/見積もりに関する問い合わせ
製品に関するお問い合わせや見積もりのご依頼は、以下のフォームに必要事項をご記入の上、送信ボタンをクリックしてください。 *は必須項目となっています
製品の詳細をお知りになりたいですか?
グローバルに展開するIARが世界各地のお客様をサポートします。製品に関するお問い合せには、常時お答えしています。


