Architecture and device agnostic
The platform for embedded development
Scale development operations with freedom and flexibility, accelerate innovation with code confidence, and simplify compliance while strengthening security.
Architecture and device agnostic
Cloud-ready, tailored for enterprises

Functional safety always included
End-to-end embedded security
Built-in security features like secure boot, encrypted code, and runtime integrity verification help protect against cyber threats, supporting compliance efforts with NIST guidance, the Cyber Resilience Act (CRA), and ETSI standards.
See how it works
See the platform in action and learn how it supports DevOps integration, built-in functional safety and embedded security, flexible licensing, multi-architecture development, and faster, repeatable builds even years after release.
Try out IAR's platform

What are you looking for?
Whether you’re evaluating IAR’s solutions, exploring developer capabilities, or just getting started — choose your path below.
IAR's embedded solutions
Explore how IAR's platform helps teams meet industry standards, ensure functional safety, and strengthen embedded security— all while accelerating development and compliance.
IAR's features and tools
What is embedded?
Driving enterprise innovation
Explore how to streamline workflows, adopt cloud-native solutions, and ensure functional safety across diverse architectures. Watch the videos to learn how IAR helps teams develop smarter and faster.
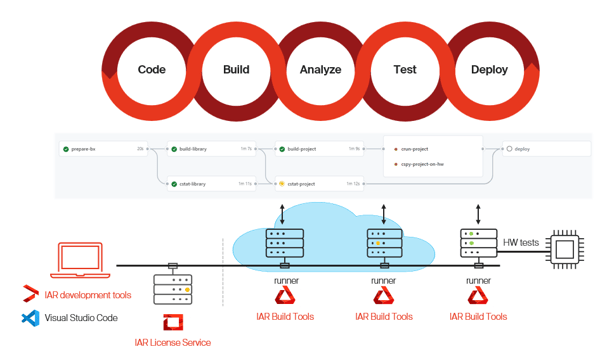
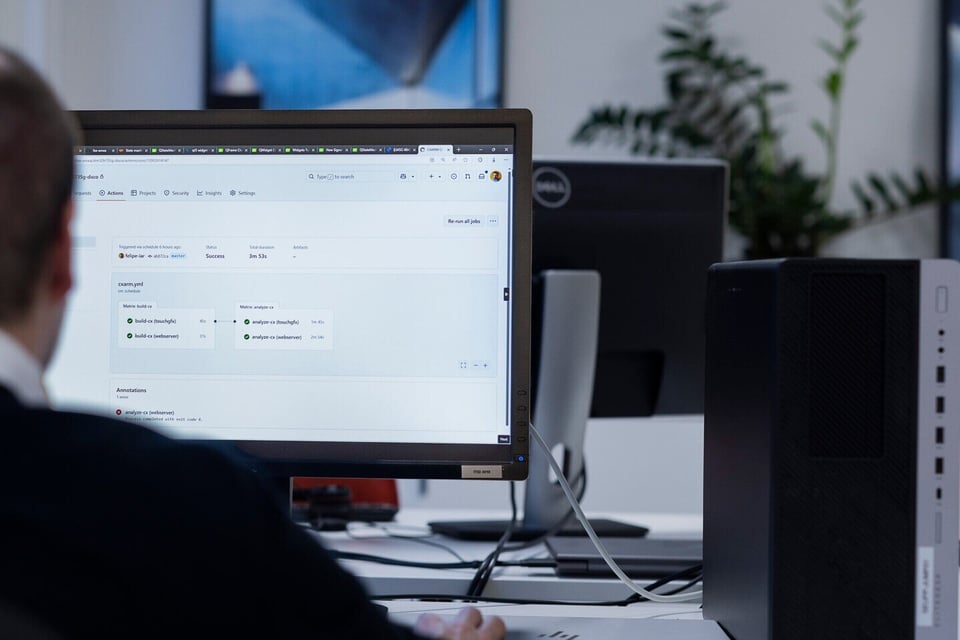
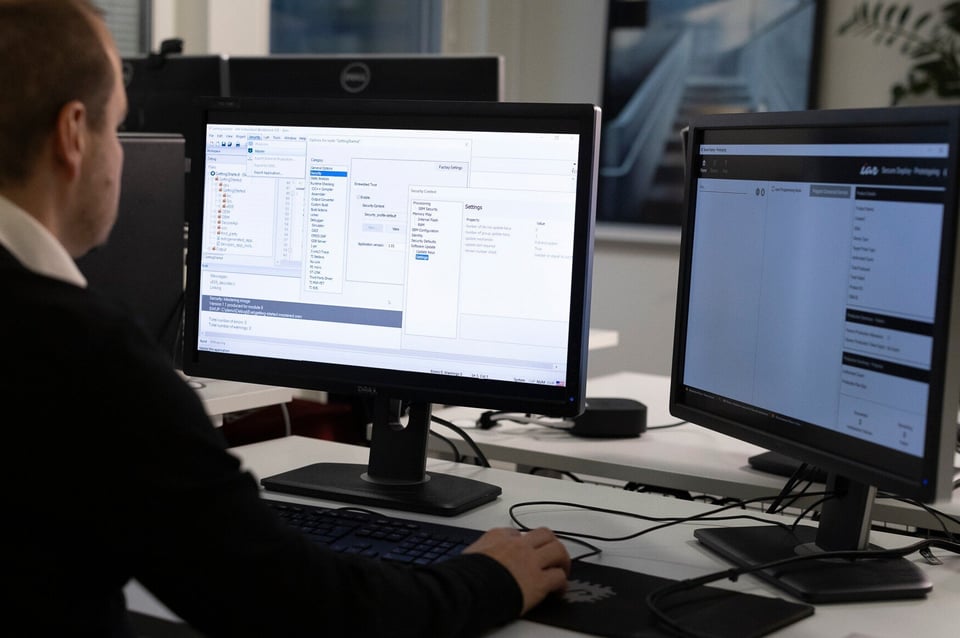
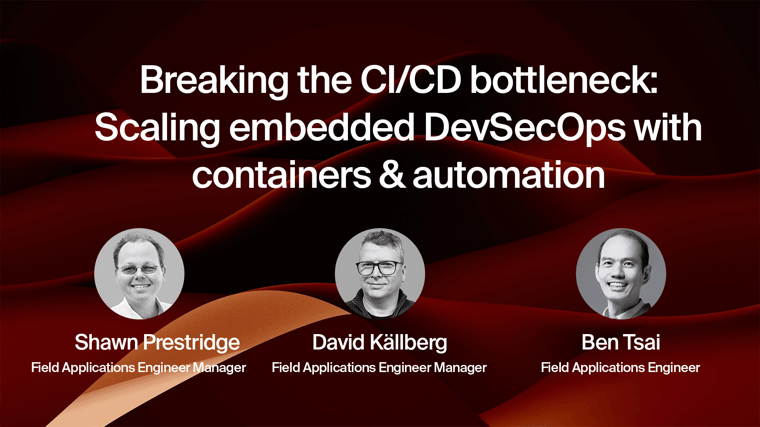
Managing diverse environments and scaling workflows across distributed teams can be overwhelming. Without standardized build environments, maintaining consistency and efficiency becomes a challenge. IAR’s platform supports containerized development and cloud-native workflows, enabling reproducible environments, automation, and scalability. With CI/CD integration suitable for cloud and container-based builds, teams can streamline development, improve collaboration, and accelerate time-to-market.
Siloed tools and vendor-specific dependencies slow down development and increase toolchain complexity. IAR’s unified platform bridges gaps across architectures, enabling seamless collaboration and efficient workflows. With advanced debugging, automation, and CI/CD integration, teams can accelerate development, improve efficiency, and reduce project delays—keeping innovation on track.
pre-certified standards
architectures
times a day you interact with a product made by one of our customers
years in business
semiconductor partners
supported devices














Solutions








Industries
IAR’s platform delivers a comprehensive palette of solutions across automotive, industrial automation, medical, machinery control, and more—ensuring development teams stay ahead of regulatory, security, and performance demands.
![[EN] Industries | Automotive](https://www.iar.com/hs-fs/hubfs/WEB%202025/Images/Industries/car%20with%20the%20lights%20on%20back%20and%20grey.png?width=600&height=338&name=car%20with%20the%20lights%20on%20back%20and%20grey.png)
IAR delivers a trusted, safety-certified platform that accelerates development, enhances reliability, and supports major MCUs and MPUs with comprehensive MCAL and AUTOSAR integration, across all...
![[EN] Products | Industries | Industrial Automation](https://www.iar.com/hs-fs/hubfs/WEB%202025/Images/Industries/Industrial%20automation/yellow_industry_robot_adobestock_213480015.jpeg?width=600&height=382&name=yellow_industry_robot_adobestock_213480015.jpeg)
Deliver high-quality, efficient, and reliable embedded systems that enhance the industrial automation processes.
![[EN] Industries | Medical](https://www.iar.com/hs-fs/hubfs/WEB%202025/Images/Industries/Medical%20doctor%20infront%20of%20screen%20with%20lungs%20%20on%20display.jpeg?width=600&height=336&name=Medical%20doctor%20infront%20of%20screen%20with%20lungs%20%20on%20display.jpeg)
IAR provides a trusted, safety-certified embedded development platform that helps medical device makers build compliant, secure, and reliable software across wearables, implantables, imaging,...
![[EN] Industries | Machinery control](https://www.iar.com/hs-fs/hubfs/WEB%202025/Images/Industries/switchboard.jpg?width=600&height=400&name=switchboard.jpg)
Unleash the power of machinery control with embedded technology. Our comprehensive range of solutions is designed to address this effectively.
![[EN] Industries | Household appliance](https://www.iar.com/hs-fs/hubfs/WEB%202025/Images/Industries/household%20appliance%20smart%20home%20screen%20on%20sofa%20table.jpg?width=600&height=338&name=household%20appliance%20smart%20home%20screen%20on%20sofa%20table.jpg)
![[EN] Industries | Household appliance](https://www.iar.com/hs-fs/hubfs/WEB%202025/Images/Industries/industries-household-appliance-4x5.jpg?width=600&height=750&name=industries-household-appliance-4x5.jpg)
Empower your embedded projects for the household appliance, from automated processes to user inputs. Our solutions ensure code quality for safe, fast, and on-time applications.
Transforming challenges into success
Get inspiration on how world-leading companies enhance their embedded development with our platform.
Read caseAlthough we increased performance, we also had to maintain power consumption, which is why we divided processing into two cores. It was a lot of work, but we were able to find a balance between improved performance and power efficiency.
Read caseQuality and certification are critical for the future of high-tech medical devices. By using C-STAT, we can improve code quality while preparing for IEC 62304-certified functional safety upgrades to meet regulatory standards.
Read caseAs firmware complexity grows, we see an increasing need for tools that help ensure software quality. Static analysis and CI tool integration will be key to improving reliability and maintaining high standards in development.
Read caseDeveloping low-power IoT systems requires defect-free, high-quality code to ensure secure integration with optimized applications and networks, while minimizing cybersecurity risks.
Read caseTo maintain high product quality, we need tools that catch defects early in development. C-STAT allows us to find bugs faster, reduce time to market, and streamline development costs, making it a core tool across our sites.
Embedded development tools and products
Product
Complete toolchain with an industry-leading compiler, debugger, and analysis tools, ensuring efficient, high-performance embedded development.
Product
Automates builds and testing in CI/CD pipelines with high-performance command-line tools, enabling scalable cloud and on-prem workflows.
Product
Detects defects, security vulnerabilities, and compliance issues early with powerful static analysis for MISRA C/C++, CERT C/C++, and industry standards
Product
Identifies runtime errors, memory leaks, and overflows, improving software reliability and debugging efficiency.
Product
Provides a secure development framework with encryption, secure boot, and device authentication for embedded systems.
Product
Safeguards embedded IP from cloning, tampering, and unauthorized access with strong encryption and device authentication.
Product
Protects firmware during production with IP protection, anti-cloning measures, and secure provisioning workflows.
Product
High-speed debugging and trace probes enabling real-time analysis, performance optimization, and fault detection for embedded applications.
Product
Enables graphical state machine modeling for efficient system design, automated code generation, and validation of complex embedded applications.
Product
Enables IAR’s build and debugging tools within Visual Studio Code, providing a modern, flexible development workflow.
Product
The IAR Eclipse plugin integrates IAR’s build toolchains and debuggers into Eclipse, enabling efficient, cross-architecture embedded development with advanced debugging.
IAR’s platform supports over 20 architectures, including Arm, RISC-V, AVR, RL78 and 8051, providing a unified toolchain that eliminates the need for switching environments.
IAR integrates with Jenkins, GitHub, GitLab, and Kubernetes, enabling automated builds and continuous testing.
By unifying workflows and enabling automation, IAR’s platform cuts down debugging time, reduces rework, and minimizes certification costs.
Vendor lock-in can limit flexibility and increase costs. IAR’s platform ensures teams can work across different microcontrollers and architectures.
IAR can provide extended maintenance, compliance updates, and migration support, ensuring software sustainability as hardware evolves.
Key take aways

Proven results

Proven results

Proven results
Webinars

On-demand webinar
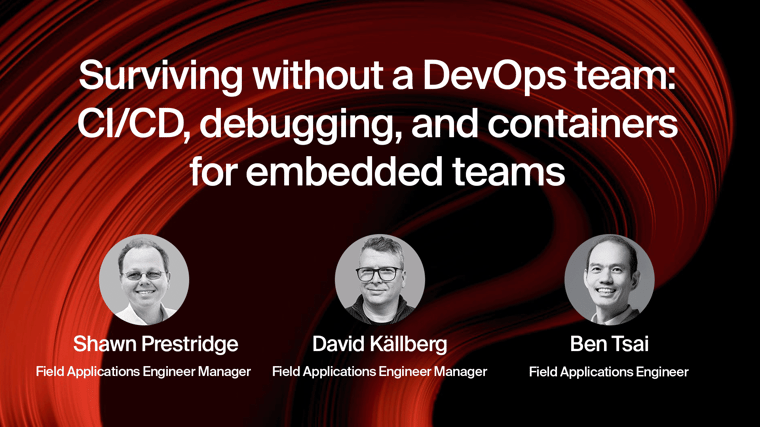
On-demand webinar
The backbone of embedded innovation
Here we have gathered questions and answers, why embedded development tools are essential for software developers.
Imagine designing a connected IoT device, an autonomous vehicle system, or a life-saving medical device. The complexity of embedded systems demands precision, efficiency, and reliability—requiring engineers to navigate hardware constraints, real-time performance needs, and compliance standards while keeping up with market demands.
This is where embedded development tools become indispensable. From code compilation to debugging, optimization, and automated builds, these tools help engineers accelerate development, reduce errors, and ensure software reliability. Among these, IAR Embedded Workbench stands out as a comprehensive solution, integrating a compiler, linker, debugger, and runtime analysis tools within a single interface.
Embedded engineers need more than just an IDE—they require debug probes, CI/CD-ready build tools, static and runtime analysis, command-line interfaces, and flexible workflows that adapt to both local and cloud-based development environments.
Embedded development tools are software and hardware solutions designed to simplify, optimize, and automate embedded system development. They enable engineers to write, compile, test, debug, and optimize firmware running on microcontrollers (MCUs) and processors.
A leading example is IAR Embedded Workbench, which integrates an optimizing compiler, linker, debugger, runtime analysis, and command-line build tools, offering a seamless development experience across multiple architectures.
Selecting the right tools ensures efficiency, compatibility, and scalability.
Key factors include:
A toolchain should provide intuitive development workflows with integrated debugging, static analysis, and automated testing.
Support for multiple MCUs and architectures (Arm, RISC-V, MSP430, AVR, Renesas RL78) is crucial. IAR Embedded Workbench supports a broad range of architectures, ensuring developers have flexibility in their projects.
Real-time debugging, trace analysis, and runtime profiling are essential for reliability.
Tools should support command-line builds (CLI), CMake, and integration with CI/CD platforms like GitHub, GitLab, and Jenkins for automated testing.
Coding standards (MISRA, CERT C), security frameworks (IEC 62443), and functional safety (ISO 26262, IEC 61508) should be built-in.
| Category | Examples |
|
IDEs |
IAR Embedded Workbench, Keil, Eclipse |
|
Compilers & linkers |
IAR C/C++ Compiler, GCC, LLVM |
|
Debuggers & probes |
JTAG, GDB, IAR C-SPY Debugger, I-jet |
|
IoT kits |
Raspberry Pi, STM32 discovery kits, ST Nucleo boards |
|
RTOS tools |
FreeRTOS, ThreadX, PX5 RTOS, Zephyr RTOS |
IAR Embedded Workbench
combines all these benefits, streamlining embedded workflows from development to production.
Choosing the wrong tools can lead to inefficiencies and costly mistakes. Here’s a quick checklist to help avoid common pitfalls:
|
Common mistakes |
Avoidance checklist |
|
Limited architecture support |
Select tools with broad compatibility (Arm, RISC-V, etc.) |
|
Weak debugging features |
Ensure real-time debugging, profiling, and trace analysis support |
|
No CI/CD integration |
Choose tools with CLI, CMake, and pipeline support |
|
Overlooking compliance needs |
Use tools that support MISRA C/C++, ISO 26262, IEC 61508 |
These kits simplify IoT firmware and hardware integration, allowing developers to prototype and deploy IoT applications.
Firmware tools help engineers write, test, and optimize code for low-power and high-performance embedded devices.
RTOS solutions manage real-time tasks, ensuring predictable system behavior in time-sensitive applications.
The next wave of embedded tools will focus on:
IAR continues to lead innovation in embedded tools, adapting to these trends while ensuring performance, security, and efficiency.

Functional safety, Code quality, Industrial Automation