Product
IAR Embedded Trust
Embedded security is included in IAR's platform
IAR Embedded Trust is an end-to-end embedded security solution designed to safeguard software, hardware, and production environments against evolving security threats.
Key benefits
IAR Embedded Trust ensures trusted execution, authenticated updates, and threat protection, enabling secure firmware deployment and lifecycle management to help developers meet security requirements with confidence.

Secure firmware updates

Security contexts
Features
IAR Embedded Trust protects against unauthorized access, cloning, and firmware tampering, ensuring trusted boot, secure provisioning, and seamless integration for enhanced device security and integrity

Immutable boot process

Secure provisioning

Seamless integration

Flexible security management
SESIP Level 1 certification

Supported devices
*Devices available upon request.
Blog posts
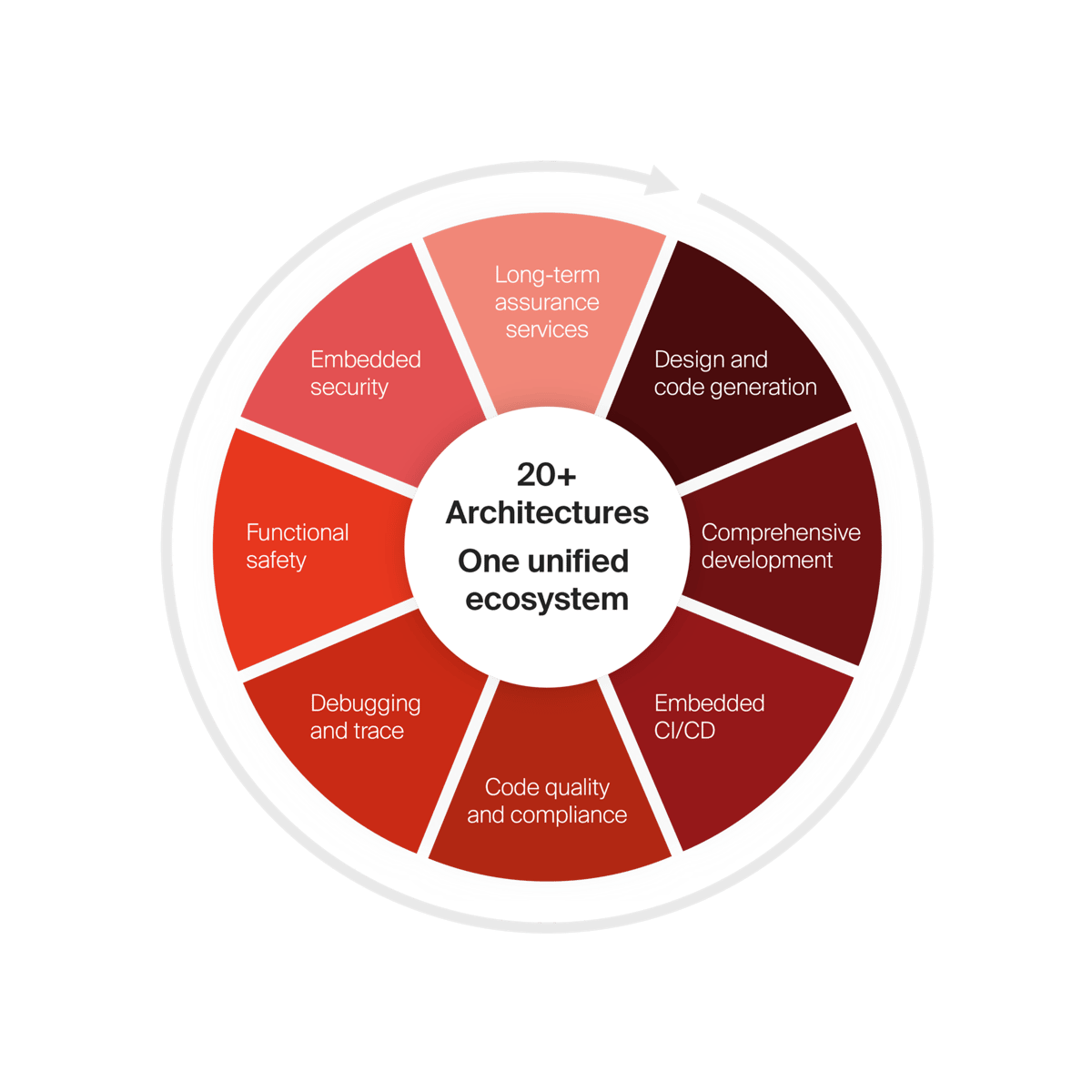
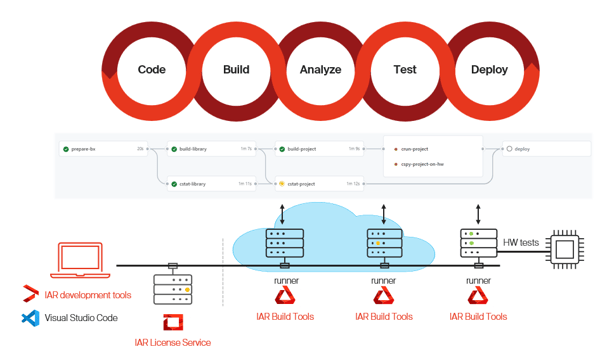
IAR embedded development platform
Get access to all
Scale development operations with freedom and flexibility, accelerate innovation with code confidence and simplify compliance while strengthening security.
- Architecture and device agnostic
- Cloud-ready, tailored for enterprises
- Functional safety always included
- End-to-end embedded security
With our platform, you get access to everything.
Try out IAR's platform
Interactive demo